Our tech
Product portfolio
We are developing a range of products born out of the latest challenges on modern battlefields. Our regular contacts with soldiers allow us to react to their needs on a weekly basis.


Fibre slicer
Fibre optics drones resist jamming and detection based on electromagnetic emissions, and can thus penetrate defenses tens of kilometers deep. We have developed and continue to improve a rapid deployable area denial system against fibre optics drones. We do not feel comfortable publishing details of our implementation, but will be glad to compare notes with partners that could help us scale up production and accelerate further reliability, speediness and robustness improvements.
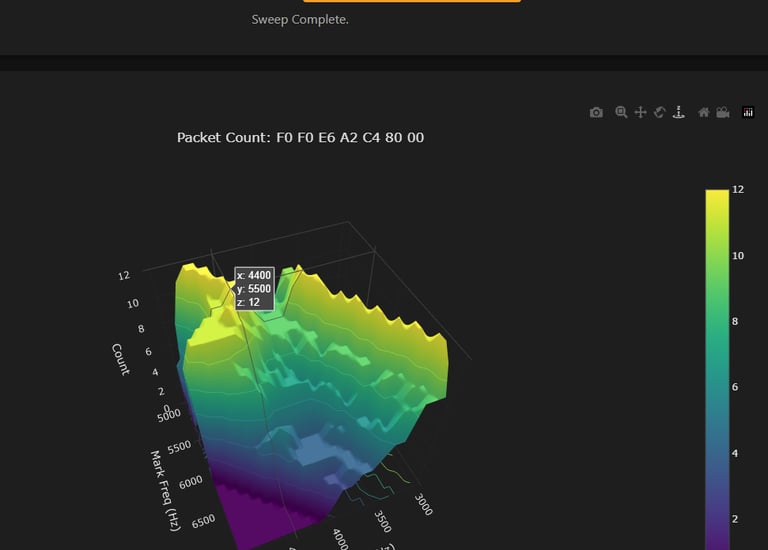
Acoustic digital modem in air
On modern battlefields, the electromagnetic spectrum is congested with friendly and adversarial jamming, and anyone emitting will be detected and localized quickly. Based on our academic work in securing wireless underwater communications in the acoustic modality, we develop solutions for use in air as well. Communicated functions would typically start with IFF and location sharing, enabling swarming and synergistic with autonomous target identification methods. We have demonstrated 100 m range in an FPV drone compatible SWaP and aim to develop further in range, low observability, and packet loss metrics.
Secure Underwater Communications
Being told to do cyber and physical security for critical offshore infrastructure we soon ended up with interoperable underwater asset authentication as a technology gap. We continue to improve our methods for layered defense with the incorporation of distributed acoustic sensing and AI-based detection.
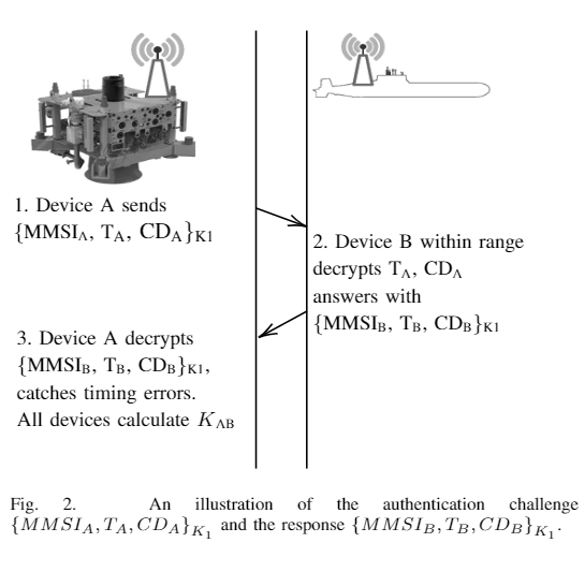
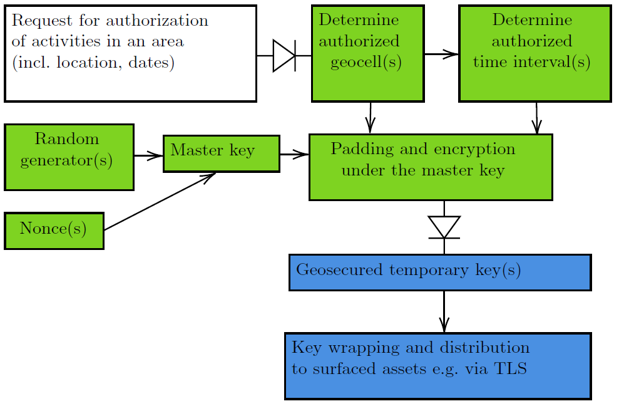
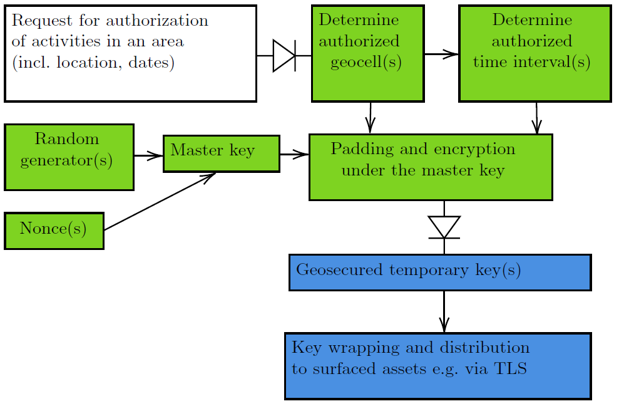
Symmetric key management
To enable secure communications including IFF, we rely on more than physical layer security, and understand why armed forces do not trust asymmetric encryption in a post-quantum world. Symmetric keys are often rotated on a high, fleet or battalion level. To suit the proliferation of attritable unmanned vehicles, we provide a method informed by the risk of losing keys despite best efforts for anti-tampering.
Secure wireless communications in the harshest environments will unlock deep values in the oceans.
Contact
Drones
contact@d-uv.com
© 2025. All rights reserved.
